Karios delivers a fully integrated Disaster Recovery (DR) solution built directly into its hyperconverged infrastructure—eliminating the need for external backup tools or complex orchestration. It unifies distributed storage, encryption, verification, and instant recovery into a self-healing, cyber-resilient platform.
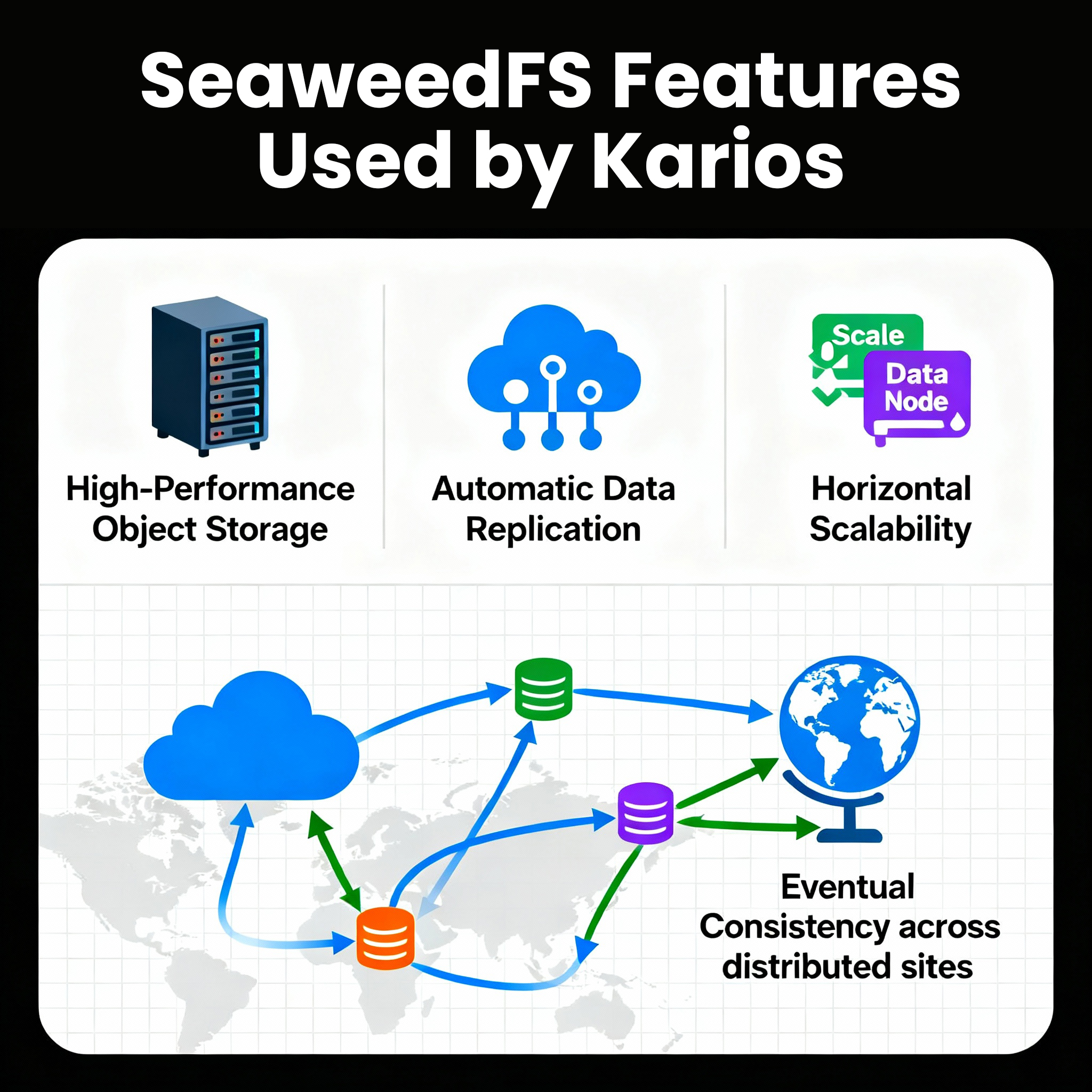
At its foundation, Karios uses SeaweedFS, a distributed object-storage layer that ensures continuous data availability and scalability across geographically separated sites. Data is automatically replicated, verified with cryptographic checksums, and instantly recoverable, guaranteeing integrity and uptime under any conditions.
Through a secure client-server model, backups are performed incrementally with AES-256-GCM client-side encryption, ensuring complete confidentiality even if infrastructure is compromised. Role-based access control and integration with Active Directory, OpenID, and PAM enforce enterprise-grade authentication and least-privilege access. Every data block and manifest is validated using SHA-256 checksums to detect corruption, tampering, or bit rot before recovery.
Karios is inherently ransomware-resistant. Immutable, write-once-read-many (WORM) backups prevent deletion or modification—even by administrators. Entropy-based anomaly detection identifies abnormal encryption activity, while air-gapped replication and delayed synchronization preserve clean recovery points across remote sites.

When disaster strikes, recovery is instantaneous. Full virtual machines or individual files can be restored in seconds through the web interface, or booted directly from backup snapshots via live-restore, allowing operations to resume immediately while full restoration completes in the background. Incremental, deduplicated backups minimize bandwidth and storage use while maintaining rapid recovery readiness.
Built-in integrity verification and cryptographic deduplication provide up to 95% storage efficiency and automatic corruption isolation. Administrators can schedule automated verification scans to continuously validate data health with minimal performance impact.
For compliance and testing, Karios supports cleanroom recovery secure, isolated environments that allow organizations to verify backup validity and measure Recovery Point (RPO) and Recovery Time Objectives (RTO) without affecting production systems. Air-gapped recovery ensures backup safety even in compromised networks.
By merging distributed storage, AI-driven automation, and integrated cyber protection, Karios redefines disaster recovery as an intelligent, autonomous service. It provides seamless resilience for private, hybrid, and edge environments ensuring data remains protected, verifiable, and instantly recoverable whenever disruption occurs.
Kairos employs SeaweedFS as one of its foundational storage layer, providing a highly scalable, object-storage infrastructure that ensures data availability, integrity, and resilience across geographically distributed sites. SeaweedFS delivers:
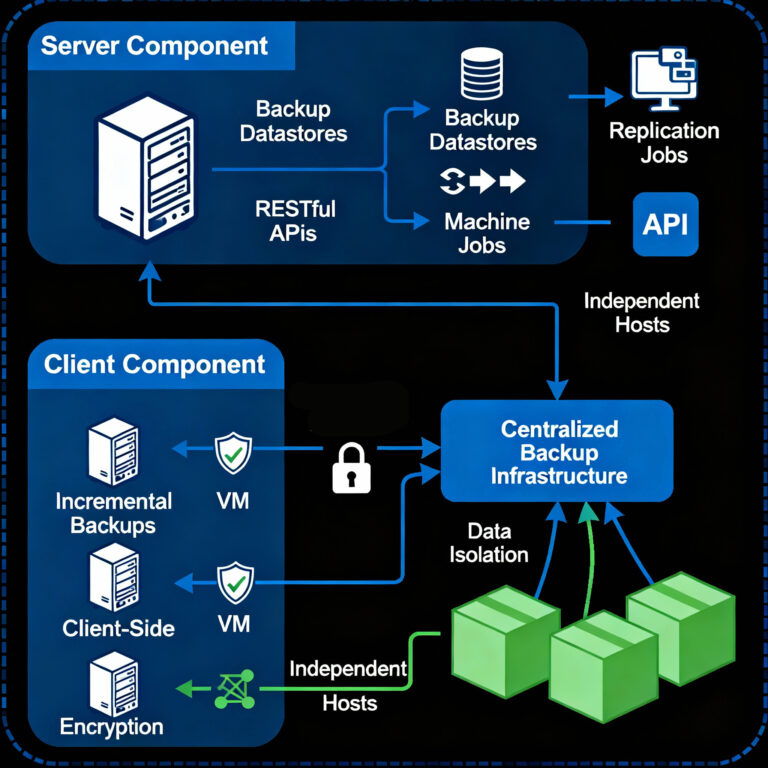
The disaster recovery solution utilizes a client-server architecture wherein:
Multi-Layered Defense Strategy
Kairos implements comprehensive ransomware protection through several integrated mechanisms that efficiently respond to cyber incidents:
Client-Side Authenticated Encryption
All backup data is encrypted on the client-side using AES-256 in Galois/Counter Mode (GCM) before transmission to the backup server. This ensures that data remains secure and useless to unauthorized users, even if the backup infrastructure is compromised. Encryption keys are managed through a hierarchical key management system, with master keys generated as RSA public/private key pairs for secure key recovery.

The platform enforces role-based access control (RBAC) with granular permissions, ensuring users are restricted to only the access levels required for their functions. Authentication is supported through multiple realms:

Data Integrity Verification
A built-in SHA-256 checksum algorithm ensures accuracy and consistency of all backup data. Within each backup operation, a manifest file containing checksums for all backup components is generated, enabling:
Immutable Backup Snapshots
Backup snapshots are stored in an immutable format, preventing modification or deletion by malicious actors. This immutability, combined with versioned retention policies, ensures that clean recovery points remain available even in the event of a successful ransomware attack.
Off-Site Protection Through Remote Synchronization
The platform enables efficient synchronization of datastores to geographically remote locations for enhanced redundancy. Only incremental changes since the previous synchronization are transferred, minimizing network bandwidth requirements while maintaining comprehensive off-site disaster recovery capabilities.
Lightning-Fast Restoration Capabilities
Kairos prioritizes recovery speed, accuracy, and flexibility, recognizing that recovery operations must be frictionless and minimize administrative burden.
Rapid Full VM Recovery
When disaster strikes, complete virtual machines can be restored in seconds through the intuitive web-based interface. The streamlined recovery process eliminates unnecessary complexity and reduces the time required to return services to operational status.
Granular Recovery Options
Rather than requiring full restoration when only specific data is needed, Kairos provides:
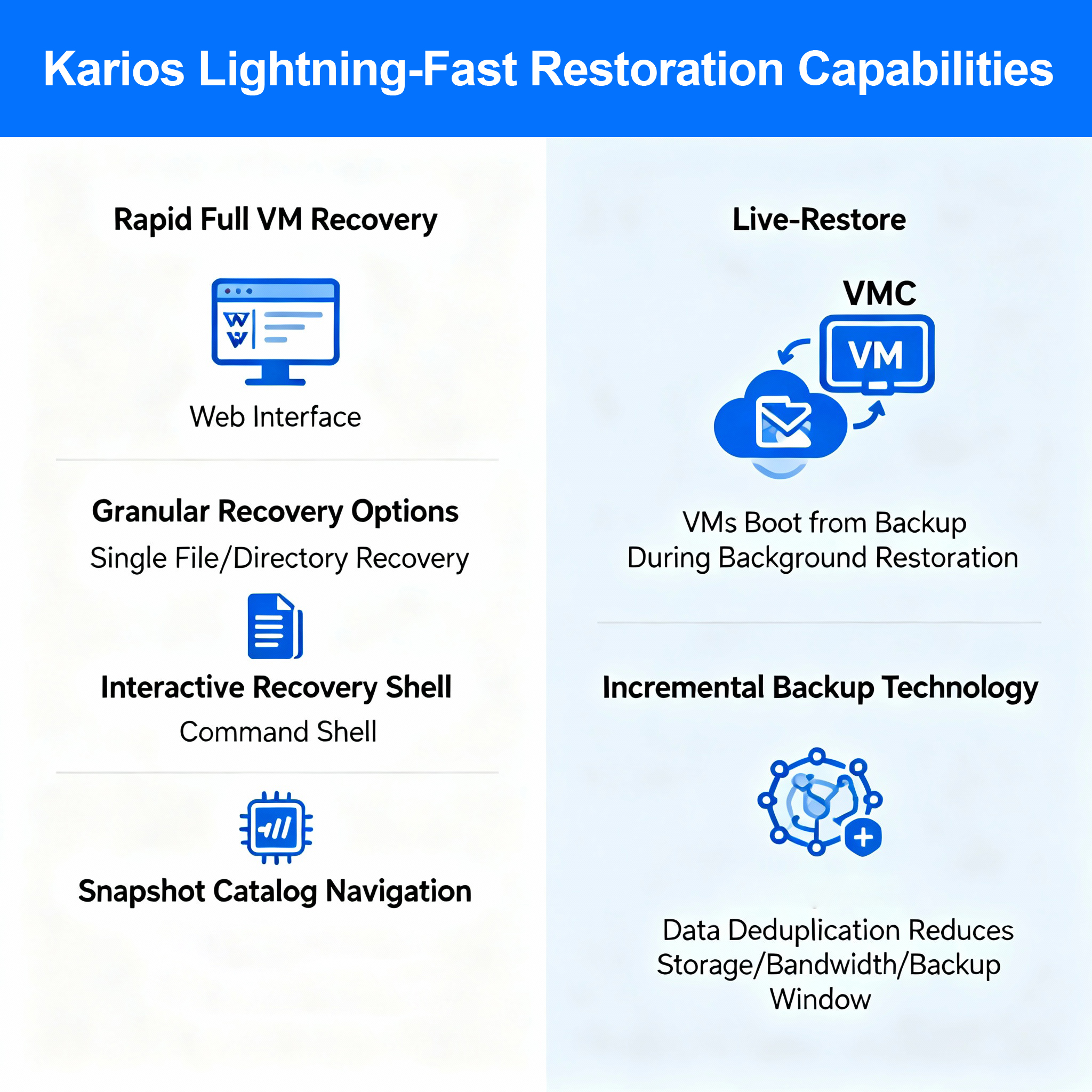
Live-Restore Functionality
An advanced feature enabling virtual machines to boot directly from backup snapshots while restoration proceeds transparently in the background. This capability dramatically reduces Recovery Time Objectives (RTOs) by allowing services to resume operation before complete data restoration is finalized.
Incremental Backup Technology
Backups are transmitted incrementally from protected systems to the Kairos backup infrastructure, where data undergoes deduplication. Since periodic backups typically contain minimal changes, only modified data blocks are read and transmitted, reducing:
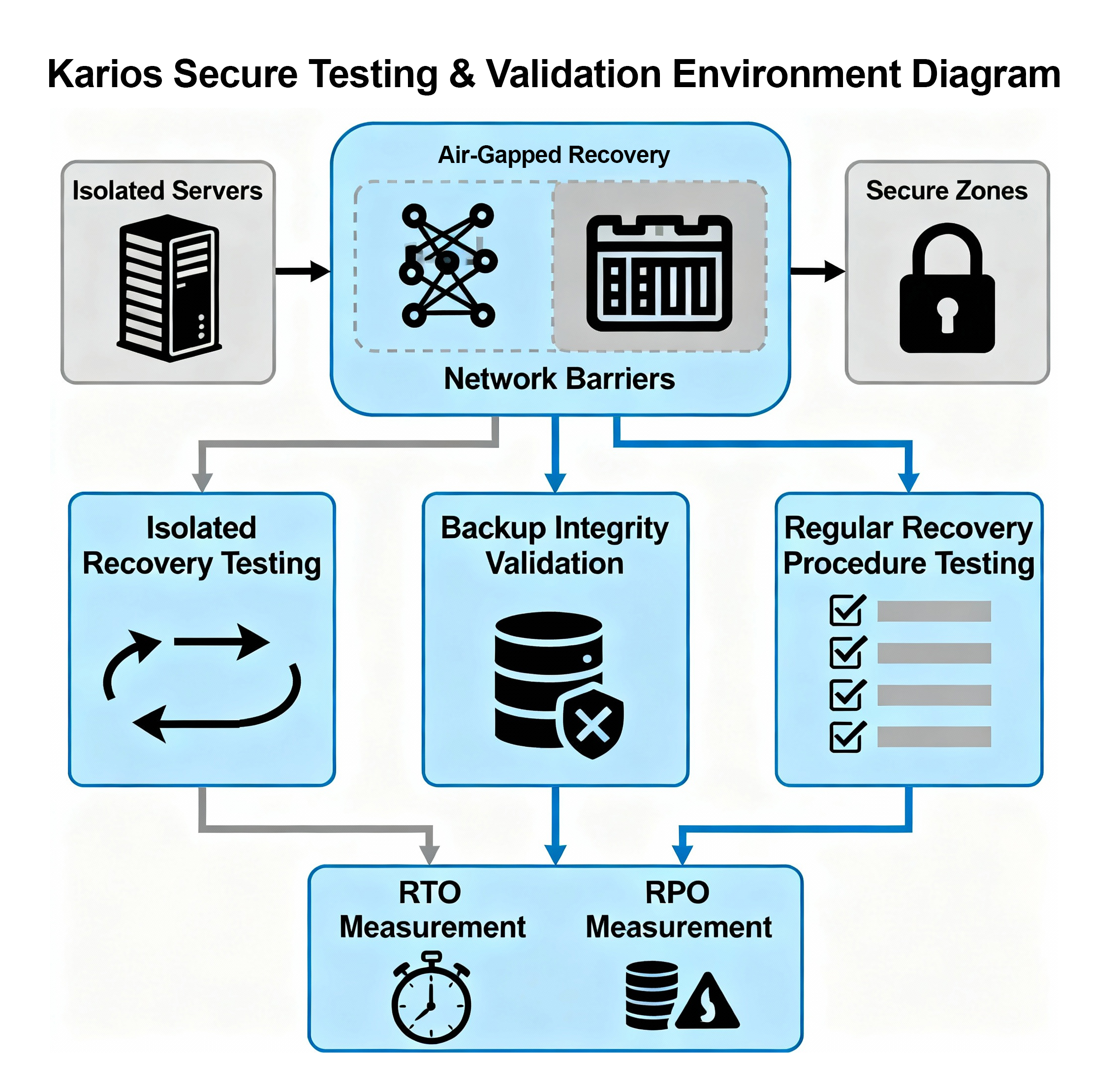
Secure Testing and Validation Environment
Kairos supports integration with cleanroom recovery methodologies, providing isolated environments for secure backup testing and validation without risk to production systems.
Isolated Recovery Testing
Backup integrity can be validated through restoration to segregated network environments, ensuring:
Air-Gapped Recovery Capabilities
The architecture supports deployment of recovery infrastructure in network-isolated segments, preventing lateral movement of threats from compromised production environments to backup systems.
The Kairos disaster recovery platform implements an advanced, multi-layered threat detection and data integrity monitoring system that provides comprehensive protection against ransomware, malware, data corruption, and unauthorized access. Leveraging SeaweedFS’s built-in integrity verification capabilities combined with intelligent behavioral analysis, the solution delivers proactive threat identification while maintaining continuous validation of backup data integrity.

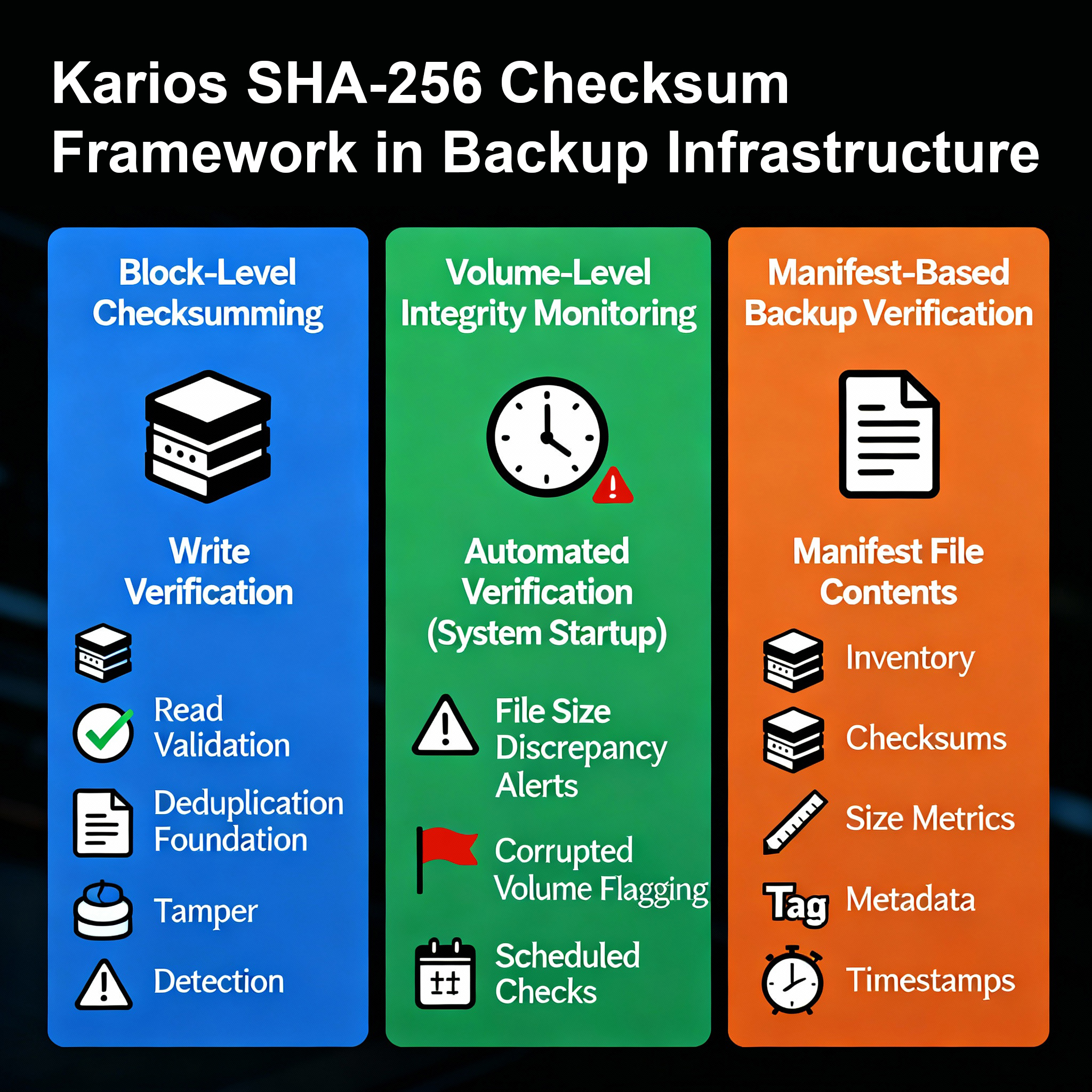
The platform employs a comprehensive SHA-256 cryptographic checksumming framework that operates at multiple levels throughout the backup infrastructure:
Block-Level Checksumming
Every data block stored within SeaweedFS receives a unique SHA-256 checksum upon creation. This cryptographic fingerprint serves multiple critical functions:
Volume-Level Integrity Monitoring
SeaweedFS performs automated volume integrity verification during system initialization and on configurable schedules:
Manifest-Based Backup Verification
Each backup operation generates a comprehensive manifest file (index.json format) containing:
This manifest enables rapid verification of backup completeness and integrity without requiring full data reads, substantially reducing verification overhead while maintaining rigorous validation standards.
Encryption fundamentally alters data characteristics, rendering it incompressible. This property provides a powerful detection mechanism integrated directly into the backup process.
Compression Ratio Baseline Establishment
SeaweedFS utilizes Zstandard (ZSTD) compression for all stored data. Under normal circumstances, most business data achieves compression ratios between 40-70%, depending on file types:
Entropy Monitoring During Backup Operations
When ransomware encrypts files, the resulting ciphertext appears random, exhibiting high entropy characteristics:
Scheduled Verification Operations
The platform enables administrators to configure automated verification schedules ensuring continuous validation of backup integrity:
Full Verification Scans
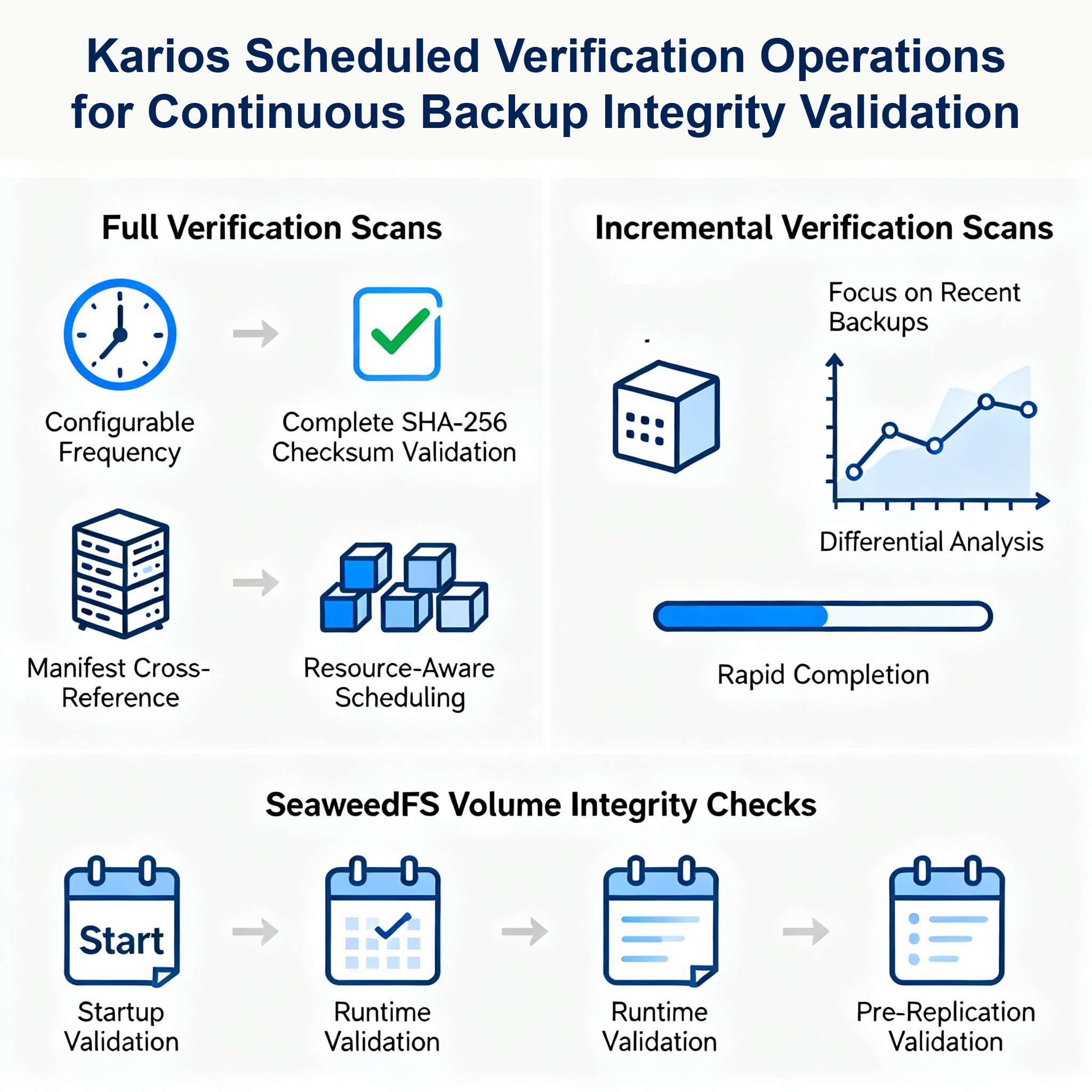
Incremental Verification Scans
Volume Integrity Checks
SeaweedFS volume servers perform integrity verification at multiple operational stages:
Immutable Snapshot Architecture
Backup snapshots are stored with immutable attributes, preventing modification or deletion even by administrative accounts during retention periods:
SeaweedFS Replication Immutability
Replicated data benefits from additional immutability protections:
Content-Addressable Storage Architecture
SeaweedFS implements content-addressable storage where data blocks are identified by cryptographic hashes:
Deduplication Integrity Verification
The deduplication system includes built-in integrity protection:
Performance Benefits
This approach is particularly effective for virtualized environments containing multiple similar virtual machines:
The Kairos disaster recovery solution implements a comprehensive, multi-layered data integrity monitoring framework that provides robust protection against ransomware, malware, and data corruption. By combining cryptographic integrity verification, entropy analysis and immutable snapshot protection, the platform ensures that backup data remains trustworthy and available for recovery operations even in the face of sophisticated cyber-attacks.
The integration of these capabilities directly into the backup workflow, leveraging SeaweedFS’s native features, provides superior detection efficiency compared to standalone security products while minimizing administrative overhead and infrastructure costs. Continuous monitoring, intelligent alerting, and automated response workflows enable rapid threat identification and coordinated incident response, substantially reducing the impact of ransomware attacks on business operations.